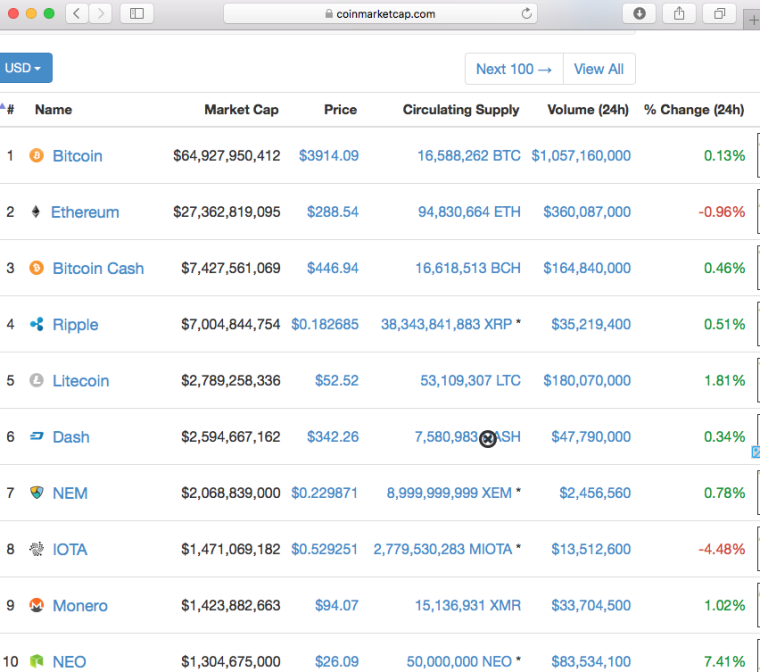
IOTA, a project on transactional settlement and data integrity for Internet of Things (IoT), is gaining popularity continuously. According to coinmarket.com, currently it is enjoying 8th position with a price of 0.5292 USD per IOTA token. It has a market cap of $1.47B, which is higher than market cap of Monero ($1.42B).
One more time the project is in news because of its alarming basic design choices . Nick Johnson, a renowned core developer of Ethereum, has published his concerns with IOTA today on medium - Why I find Iota deeply alarming. According to him,
-
Iota shows a lack of good technical judgement - Arguments provided by the team is not good enough for the use of balanced ternary, a numeral system with 3 digits, -1, 0 and 1, rather it is imposing a large computational overhead.
-
Iota disregards cryptographic best-practices - Neha Narula and team already demonstrated the predictable result of Iota’s novel choice of numeral system in Cryptographic vulnerabilities identified in IOTA.
-
Iota is a bad actor in the open source community - Sergey Ivancheglo, Iota’s cofounder, claims that the flaws in the Curl hash function were in fact deliberate; that they were inserted as ‘copy protection’, to prevent copycat projects, and to allow the Iota team to compromise those projects if they sprang up. But it’s an admission of hostile intent towards the open-source community, If Iota wish to discourage copycats, they can license their code in a manner that prohibits the kinds of reuse they are unhappy with, or keep it closed source, as they have done with their centralised coordinator.
-
Iota’s integrity guarantees lack rigor - Iota, utilizes a ‘tangle’ — a directed acyclic graph of transactions — with no single head, instead of blockchain. Each transaction is secured using a proof of work, but this PoW function has a fixed difficulty. Further, unlike blockchain-based systems such as Ethereum and Bitcoin, the difficulty of the proof of work is not adaptive. This means that the security of the tangle directly depends on the number of transactions being processed, and that there is no way to adapt the security level to real-world conditions.
For more updates, technical blogs and general discussion on Blockchain Technology and Ethereum, please join us at our Website, reddit, Facebook, Medium, steemit and follow us at Twitter. Please email your suggestions.